Brandon Wiley is President of Operator Foundation, an organization that promotes internet freedom, open communication and global internet security through technology development, deployment, and education. The organization develops technologies to enable access to credible and relevant information and open communication around the world. I.e. to CATS, credible and topical sources.
Dr. Wiley is a peer-to-peer pioneer who creates tools to circumvent Internet censorship. In 1999, he co-founded the Freenet project to create a censorship-resistant publishing platform. Since then, he has worked on core technologies, such as BitTorrent, Tor, and OpenVPN. He has a PhD in Information Studies, specializing in the use of machine learning and Bayesian statistics to create polymorphic network traffic encodings to defeat Deep Packet Inspection filtering techniques. He is a co-author of the book “Peer-to-Peer: Harnessing the Power of a Disruptive Technology”, a Google Ideas Research Fellow, and an Open Technology Fund Rapid Response Research grant recipient.
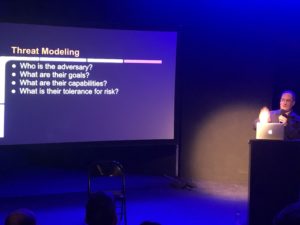
In this talk, at Actlab 2019, he discusses exfiltrating data from restrictive networks, a skill that every hacker can use. As firewall filtering techniques become more advanced, so must we advance the methods for defeating firewalls. This talk presents decades of research on network traffic obfuscation in a format which will be both accessible to beginners and illuminating for experts. Starting with a brief introduction on the history of the approaches of those that would build firewalls versus those that would circumvent them, the talk then proceeds into the specialized area of network protocol obfuscation techniques. After this introduction familiarizes and refreshes the audience on the topic, the core of the talk discusses a practical approach to defeating adversaries that would seek to break the Internet by restricting network traffic. An overview of the full methodology will be presented, from threat modeling on through to implementation and testing.